Define exactly what each tool call is allowed to do.
Build policies around the fields that matter — amount, branch, environment, SQL text, recipient, customer tier. Allow, deny, rate-limit, or require human approval before execution.
PolicyLayer enforces your rules on every MCP tool call before it runs. Deterministic checks, not prompts.
They can move money, reconfigure infrastructure, merge code, query private data, and contact customers through tools. Prompts are not control. Enforcement has to sit at the execution boundary.
stripe.refund_payment destructive shopify.create_payout mutating coinbase.list_transactions read aws.terminate_instance destructive cloudflare.update_dns mutating vercel.list_deployments read github.force_push destructive gitlab.merge_request mutating linear.list_issues read postgres.drop_table destructive supabase.execute_sql mutating mongodb.list_collections read slack.delete_channel destructive sendgrid.send_email mutating intercom.list_users read okta.disable_account destructive atlassian.modify_project mutating notion.list_pages read See how PolicyLayer governs each surface: payments, code, data, infrastructure, and customer ops.
Drop PolicyLayer into your MCP request path. Your agents keep their tools; you decide what each call can do.
Each agent, person, environment, and workflow gets its own labelled grant. Attach different policies. Revoke any one without breaking the rest.
Different agents, environments, and people can all run different policies against the same MCP server. One upstream credential, many scoped grants.
Kill one token immediately without rotating the upstream API key or redeploying every client. Offboard a person or contain an incident in seconds.
Every decision records which grant made the call, which policy applied, and which rule allowed or denied it. Forensic trail without storing secrets.
New grants start with only the tools and actions you explicitly allow. New upstream tools never silently become available to existing agents.
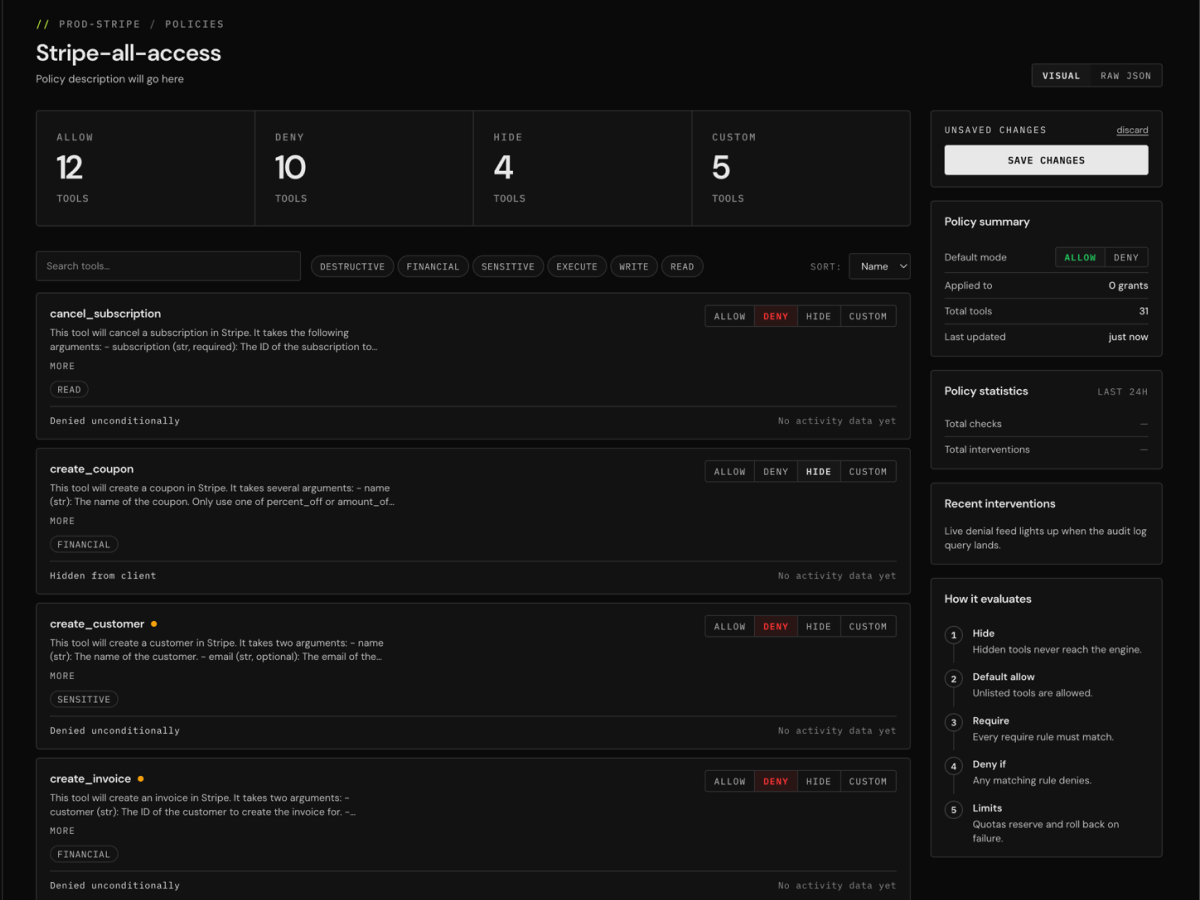
Build policies around the fields that matter — amount, branch, environment, SQL text, recipient, customer tier. Allow, deny, rate-limit, or require human approval before execution.
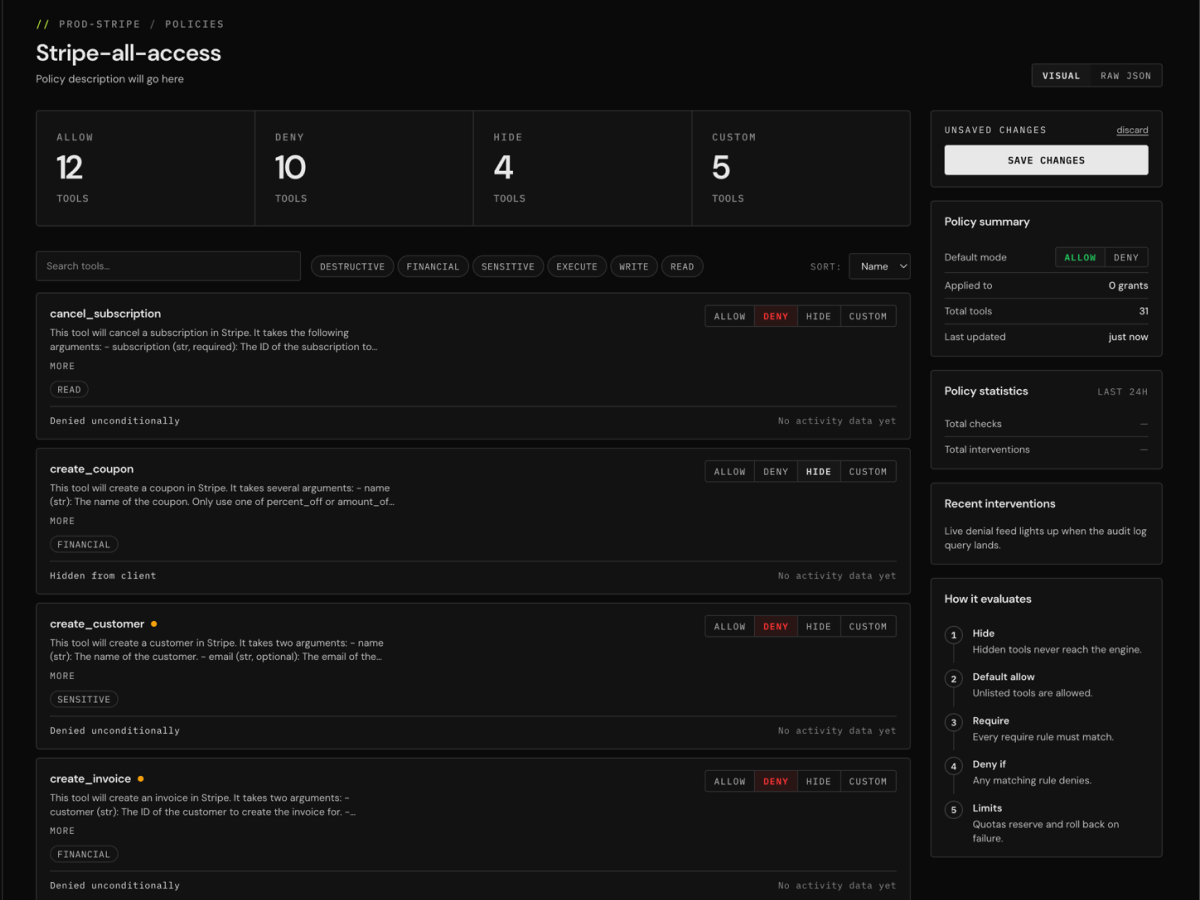
Every server's tools auto-discovered via the upstream's tools/list and surfaced in the dashboard with full schemas. Edit policy directly per tool.
Every call recorded with the grant that made it, the outcome, the policy version that decided, and the rule path that fired. Append-only. Filter by server, grant, or outcome.
Every save creates an immutable policy version. Roll back without losing history. Diff what changed, who changed it, and when.
Static API keys and OAuth tokens stored AES-256-GCM encrypted at the column level, decrypted only on the path to the upstream MCP.
Upstream credentials cannot be read back through the dashboard or API once saved. They never appear in events, logs, or the bearer tokens issued to clients.
Ambiguous grant, policy, or upstream states resolve to deny, not allow.
Decision events and policy versions are append-only by design. The audit log you build can't be edited or removed from inside the app.
Pre-classified tools across the MCP servers your agents already use. Start from deny-by-default instead of a blank page.
Anything that speaks the MCP protocol — Stripe, GitHub, Postgres, AWS, Slack, Cloudflare, Sentry, Vercel, Linear, Notion — plus self-hosted and community servers. If your client can connect to it over MCP, you can route it through PolicyLayer.
No. Your MCP client connects to a PolicyLayer URL with a grant token — issued per agent, person, environment, or workflow. Same tools. Same schemas.
A prompt asks your agents to behave. PolicyLayer enforces your rules so they can't misbehave. Every call is evaluated before execution.
PolicyLayer accepts static API keys or managed OAuth with full discovery, registration, and refresh. We store credentials AES-256-GCM encrypted at the column level, decrypted only on the path to the upstream MCP. Once saved, no one — including us — can read them back through the dashboard or API. They never appear in events, logs, or the tokens issued to clients. Your users and agents authenticate to PolicyLayer with their own scoped tokens, never the raw upstream credential.
Teams running multiple MCP servers in production: AI engineers, platform engineers, security teams, and technical leaders who need deterministic control over agent actions.
Sign up at app.policylayer.com, register your first upstream MCP server, define a policy, and point your AI client at the PolicyLayer gateway. Most teams have their first policy enforcing in under 10 minutes.
Route your MCP servers through PolicyLayer and every tool call is checked against your policy before it runs — allow, deny, or require approval. Per-identity grants. Full audit log. Live in minutes.
Free to start. No card required.
4,600+ MCP servers and 31,000+ tools scanned and risk-classified.